How to Get an A+ on SSL Labs Report
As a follow up to my post on cheap SSL certificates, I learned that the certificate wasn’t the reason I was getting an A- on the Qualys SSL Labs test. But after a few configuration changes, I achieved the coveted A+ grade.
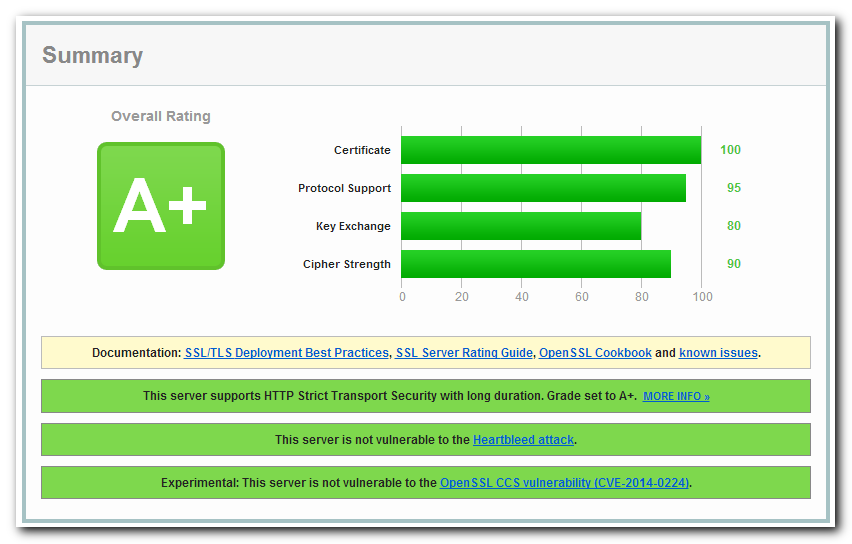
First, find out your current grade by entering your web site here. If it’s an A+, congratulations! If not, continue reading.
This is the NGINX configuration I’m using (in the server block):
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
ssl_prefer_server_ciphers on;
ssl_ciphers "EECDH+ECDSA+AESGCM EECDH+aRSA+AESGCM EECDH+ECDSA+SHA384 EECDH+ECDSA+SHA256 EECDH+aRSA+SHA384 EECDH+aRSA+SHA256 EECDH+aRSA+RC4 EECDH EDH+aRSA RC4 !aNULL !eNULL !LOW !3DES !MD5 !EXP !PSK !SRP !DSS";
ssl_session_cache builtin:1000 shared:SSL:10m;
ssl_stapling on;
ssl_stapling_verify on;
resolver 8.8.4.4 8.8.8.8 valid=300s;
resolver_timeout 10s;
add_header Strict-Transport-Security max-age=63072000;
add_header X-Frame-Options DENY;
add_header X-Content-Type-Options nosniff;
The only browser this doesn’t support is IE 6 on Windows XP, but I’m okay with that. Windows XP is no longer supported and IE 6 is just about dead (thank goodness). If you’re daring, use the above configuration or the configs at CipherLi.st and hope for the best. I opted for the legacy support option (click on the “Yes, give me a ciphersuite that works with legacy / old software.” link). And CipherLi.st has example configurations for Apache and Lighttpd.
If you want to learn more about what each of the options do, I found these two tutorials helpful:
[…] checked my grade on SSL Labs and found it had dropped from the coveted A+ to an A due to the use of SHA-1. I’m pleased to see they’re keeping the test updated. […]